A Sybil attack happens when one person creates many fake identities to gain control over part of a crypto network. Whether you’re using crypto apps, voting in DAOs, or just holding tokens matters.
Crypto hacks, in general, are becoming more advanced and expensive.
This guide explains Sybil attacks, how they happen, where they strike, and how to protect yourself without needing a technical background.
- Show Full Guide
What is a Sybil Attack in Crypto?
In crypto, the consequence of such an attack is that it can mess with how networks make decisions, reach consensus, or validate transactions. It’s a way to cheat systems that rely on trust between many users.
You’ll often notice Sybil attacks mentioned in connection with blockchain voting, peer-to-peer platforms, or decentralized apps. They can affect how secure, fair, or reliable those platforms are.
This kind of attack is one of the key threats (and flaws) associated with decentralized systems, thus every crypto user should know what it means and how it manifests.
Why it’s called a “Sybil” Attack
The name “Sybil attack” comes from a 1973 book about a woman named Sybil who was diagnosed with having multiple personalities.
In tech, the term stuck as a reference to the idea of one actor splitting into multiple identities.
That’s precisely what happens in a Sybil attack: one user pretends to be many, tricking a system that depends on users being separate and independent.
Understanding Sybil attacks on blockchain networks
Blockchains rely on the idea that users are separate and play fair — Sybil attacks break this system by flooding the network with fake identities.
This makes this especially powerful because it can shift power, control votes, and manipulate how the network runs.
However, to understand the extent of these attacks, it might help to break down the different ways a Sybil attack can work.
1. Direct Sybil Attacks
In this specific attack, fake accounts interact directly with the real accounts.
There is no middle layer, no disguise. It is literally just a flood of false identities trying to overwhelm or influence the honest participants.
A perfect scenario is a peer-to-peer network where users can share files. If one person creates hundreds of fake nodes, they can flood the network, slow it down, or even block access to certain files.
Direct attacks like these mess with how nodes connect, how blocks spread, or how decisions get made.
The attacker shows up everywhere, pretending to be different users, but it’s really just one source.
These attacks are simple to launch, especially on open networks with no barriers to entry. This is why they’re often the first method attackers attempt.
2. Indirect Sybil attacks
Indirect Sybil attacks are more complex to spot because they do not directly interact with honest users.
The attacker often uses their fake identities to influence parts of the system quietly.
Usually, by flooding a network with fake validators or voting nodes. They won’t stop until they can tip decisions in their favor.
In a decentralized application (dApp), these actors could use these identities to spam forums, fake reviews, or build fake trust scores. The idea is to create the illusion of consensus or support when there’s none.
And these attacks can go unnoticed because there’s no immediate, obvious interference.
That makes them especially risky for systems that depend on user feedback or crowdsourced input to make key decisions.
3. 51% attack
A 51% attack is when one group or person controls over half the network’s power, like mining or validating blocks.
It’s not always considered a Sybil attack, but it shares the same trick—one actor gaining too much influence, which means a Sybil attack can cause it.
Once someone controls most of the system, they can rewrite parts of the blockchain, double-spend coins, or block new transactions from confirming.
This breaks blockchain’s fundamental promise: no single user can take over.
These attacks usually target smaller or newer blockchains, where the cost of taking over is lower. This is part of why projects implement systems that decentralize power early on—to avoid being an easy target.
Sybil attacks differ from 51% attacks in that they involve creating many fake identities to gain influence. 51% attacks require controlling most of a network’s computational power or stake to alter the blockchain.
Where do Sybil Attacks happen in crypto?
Sybil attacks can appear almost anywhere in crypto where trust and identity matter. They target the weak spots in systems that rely on user input, shared decisions, or open access.
Peer-to-peer networks
Peer-to-peer networks are especially vulnerable. These networks depend on users connecting directly to each other. An attacker can flood the system with fake nodes, taking over routing paths or blocking access to real peers. That breaks the flow of data and can isolate or confuse honest users.
Distributed consensus protocols
Distributed consensus protocols – how blockchains agree on what’s true—can also be manipulated. Sybil nodes can disrupt this process, delay confirmations, or push false data through. When too many fake participants flood the system, trust breaks down fast.
Blockchain voting and governance
Blockchain voting and governance is another target. In many crypto projects, users vote on proposals using tokens or credentials. If someone creates a swarm of fake identities or buys up influence cheaply, they can push through harmful changes or block upgrades that the majority wants.
Sybil attacks can be especially dangerous in on-chain governance, where fake accounts can influence proposals or funding. If you’re new to this, here’s a breakdown of what governance tokens are.
Tracking Sybil attacks
A blockchain project called ‘Bubblemaps’ is tracking sybills as well as exploits that occur in the market. On November 12, it identified a Sybil attack that took place during the presale of MegaETH (the token is not tradable yet at the time of this writing).
Despite the KYC requirements, a limit of one wallet per user, and a $186,000 per-user limit, investing $5 million via more than 20 wallets violated these restrictions.
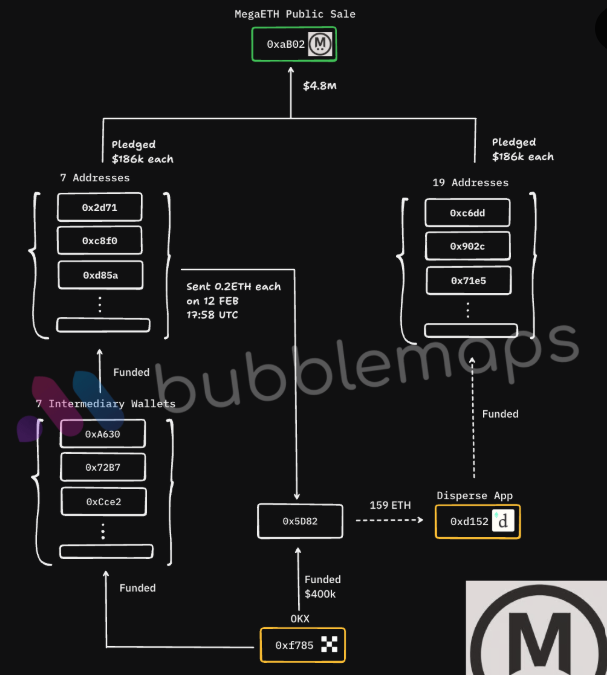
Bubblemaps reports sybills and other exploits on its X account and official website. The attack may have been carried via family members IDs or colleagues to bypass the KYC restrictions.
The risks of a Sybil Attack
Sybil attacks don’t just mess with numbers—they break how peer-to-peer systems are supposed to work.
- Network disruption is one of the most immediate effects. Flooding a system with fake nodes can slow things down, block communication, or overload honest participants. This can isolate users or make basic functions stop working.
- Manipulating votes or consensus is another serious risk. Blockchains often rely on majority agreement to make decisions. If fake identities gain voting power, they can approve shady proposals, block good ones, or rewrite agreements that were supposed to be permanent.
- Attacking trust in decentralized systems causes long-term damage. People use crypto because they want systems without central control. Sybil attacks flip that promise, giving one actor hidden control. That kind of manipulation can drive users away.
Examples of Sybil attacks in blockchain networks
Sybil attacks have left their mark on the crypto industry, demonstrating how fake identities can cause significant damage.
- Monero Attack (2020–2021)
Monero faced a Sybil attack targeting its peer-to-peer network between 2020/2021. The attack involved a single attacker deploying thousands of fake nodes to monitor transaction flows. The goal was to weaken Monero’s privacy by surrounding users’ connections and observing broadcast behavior.
- Ethereum Classic Attack (2019)
In January 2019, Ethereum Classic suffered random but repeated 51% attacks that involved attackers flooding the network with multiple fake mining nodes. These Sybil identities enabled them to reorganize blocks, allowing for double-spends and disrupting network reliability.
Protecting your cryptocurrencies from Sybil attacks
Keeping your crypto safe can involve studying how networks defend against Sybil attacks. Since these attacks target the system’s trust, it is useful to know how blockchains use smart defenses to keep fake identities out.
Before we discuss defenses, ensure you understand what keeps your funds safe. Your private key is one of the most critical tools for protecting access to your wallet.
Common defenses against Sybil attacks
There’s no single way to block a Sybil attack—networks usually layer multiple strategies together. Some defenses are complex, like analyzing wireless signals or using math-heavy tools like “random walks.
But you don’t need to get into all that. Let’s only focus on three easier-to-understand approaches that are more widely used:
1. Identity verification
The most direct way to counter a Sybil attack is to ensure that each participant is a genuine person—not a fake account.
This happens in a few ways. Some platforms use phone numbers, emails, or credit cards to confirm your identity. Others go deeper, asking for government ID or tying access to a verified real-world identity.
Some systems spread this process out across a network, using cryptography (math that keeps info secure) to check if someone is legit—all without revealing who they are.
It’s not bulletproof, but it raises the bar enough to stop most low-effort attempts.
2. Reputation systems
You’ve probably seen a trust score or karma rating online. Some crypto networks use a similar concept to filter out bad actors. The longer you’ve been around, and the more helpful or honest you’ve been, the more trust you earn.
Your reputation may influence how much your vote counts in decisions or whether people are willing to interact with you.
One example is with the Delegated Proof-of-Stake (DPoS). In this setup, only a few trusted users help make key decisions, much like electing reps instead of letting everyone vote. This limits the impact of fake accounts since they start with no reputation and work hard for trust.
It’s not a perfect system as reputation can be gamed—but it makes Sybil attacks harder to pull off at scale.
3. Resource testing
This strategy route requires you prove you’re using real computer power, time, or money—something fake identities can’t easily fake.
You might be asked to solve a puzzle (like Bitcoin’s mining process) or pay a small fee to join.
The logic is simple: if it costs time or money to act, attackers can’t cheaply spin up thousands of fake nodes. Some systems also look at your physical location or network setup. If 100 identities come from the same place, that’s a red flag.
This kind of check doesn’t always stop a determined attacker, but it slows them down and makes large-scale Sybil attacks expensive.
Often enough to keep things fair for everyone else.
An ideal example would be with Proof-of-Burn, where some blockchains require users to destroy coins as proof of commitment, which fake accounts would struggle to afford.
Or consider Ethereum’s gas fees, where every transaction costs a fee, so launching Sybil attacks at scale would quickly rack up massive costs.
Top crypto mechanisms’ defenses against Sybil Attacks
- Proof-of-Work (PoW), made popular by Bitcoin, works by making these attacks very costly. Miners need to solve complex puzzles using computing power to join the network, and creating many fake identities means huge energy and hardware costs. This often discourages attackers looking for an easier way to flood the system.
- Proof-of-Stake (PoS) is different because it ties the influence to the amount of crypto you own and lock up. It’s not enough to create fake accounts. You need real stakes in the system. This makes it expensive and risky to control multiple identities.
Most consensus algorithms use reputation systems and identity verification, which add layers of trust.
Some networks track user behavior or require identity proofs before granting privileges, which limits how easily one person can create fake accounts and gain power.
Why Sybil Attacks matter for crypto beginners
If you’re new to crypto, Sybil attacks might sound technical, but they can hit you where it hurts: your wallet and apps.
Fake accounts can mess with the dApps you use daily. A single attacker running hundreds of fake profiles can flood systems, sway votes, or block real users.
That means features you rely on could stop working—or worse, get manipulated behind the scenes. This usually affects token airdrops or reward programs. Regular users miss out if attackers grab most of the tokens using fake accounts.
And when blockchains get overloaded with Sybil activity, transaction fees spike or confirmations slow down. You end up paying more and waiting longer.
Final thoughts
There’s no silver bullet for Sybil attacks. As long as networks rely on user trust, someone will try to fake their way in. But that doesn’t mean you’re helpless.
Blockchains are already fighting back with systems like Proof-of-Work, Proof-of-Stake, and identity checks. And the more you know, the harder it is for attackers to trick you.
For beginners, the best defense is paying attention—especially on platforms that give power or rewards with no checks in place. Fake accounts thrive where no one’s watching.
While Sybil attacks target systems more than individuals, weak wallet practices can still make you vulnerable.
FAQs
What is a Sybil attack in simple terms?
Are Sybil attacks still a risk in 2025?
Can Sybil attacks happen in Bitcoin?
Is it possible to prevent Sybil attacks?
Can Sybil attacks be used to manipulate airdrops or token distributions?
References
The Sybil Attack | The Free Haven Project
Sybil Millionaires: How Airdrop Hunters Trick Projects and Snatch Fortunes | CoinDesk
The Chainalysis 2025 Crypto Crime Report | Chainalysis
Bitcoin and the 51% Attack Explained | Investopedia
Blockchain has high potential but be aware of cyber threats | WEForum





